Use of Passive DNS in multidisciplinary teams’ collaboration
DNS has become a fundamental protocol that fuels the Internet. As a result, DNS is often an underappreciated source of cyber intelligence. In this blog post, you’ll learn how to search the Internet using historical passive DNS data, specifically Farsight DNSDB, to uncover suspicious activities, malicious infrastructure and other DNS-related connections that cannot be done by any other methods in principle.
DNS Search at Work
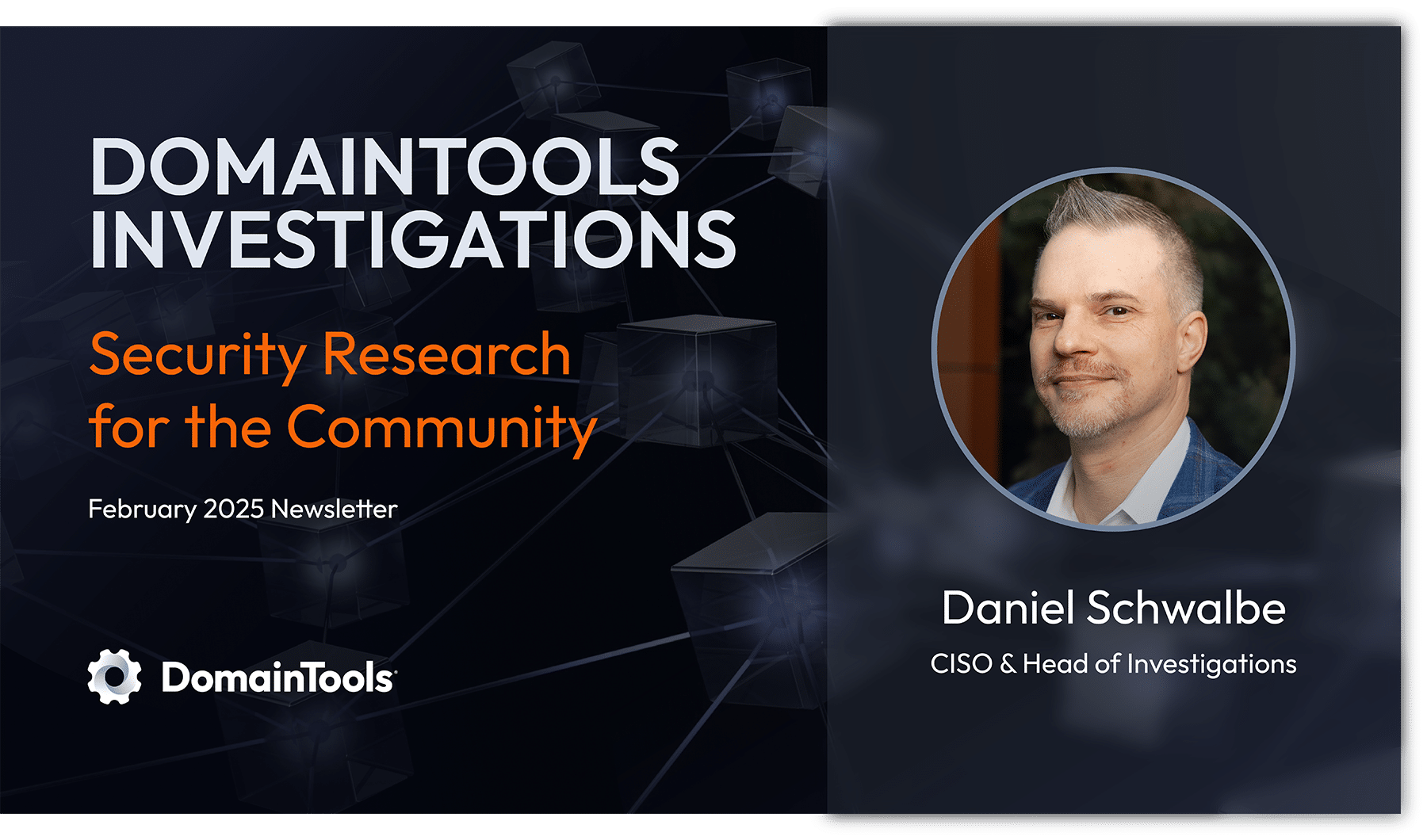
Let’s consider a real-life example using hypothetical data. Your CEO received an email that passed all your defences, but, in fact, was a well-crafted spear phishing attack. Fortunately, your CEO recognized that it was a phishing mail before she clicked on a link – all due to your organisation having great cyber awareness campaign! Yet the CEO wants to know — how did it slip through your defences?
First, the CEO calls the company CSO, who checks the email header – it passed Domain-based Message Authentication, Reporting and Conformance (DMARC), the email authentication framework, checks. Next, the CSO checks the sender’s domain via lookup, but the domain is already long gone!
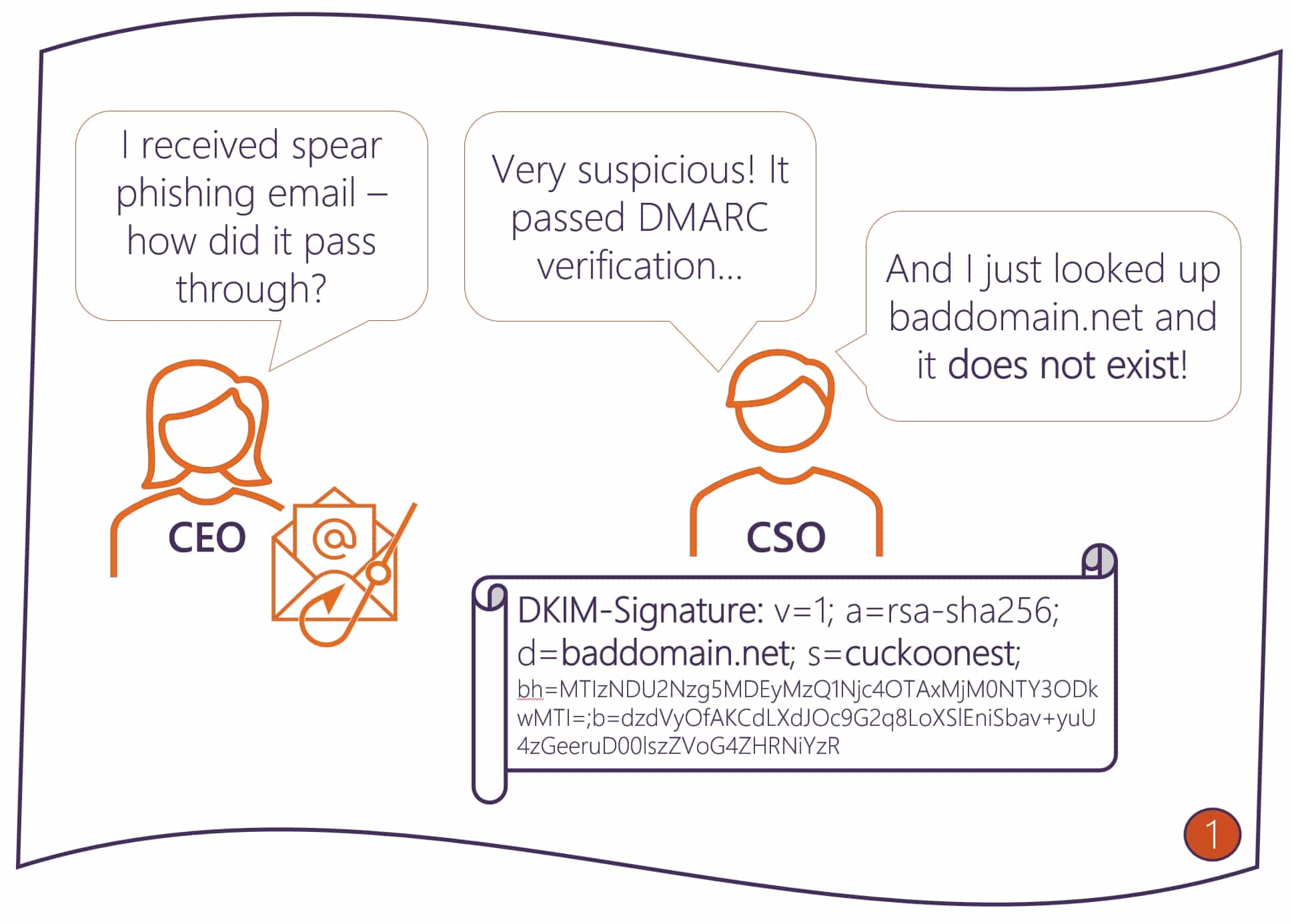
And now the question is – without the domain, is there anything we can do to progress the investigation? The CSO poses the question to his Digital Forensics and Incident Response (DFIR) team. Luckily, the team knows about Passive DNS, and, in the fraction of the second, they obtain the DomainKeys Identified Mail (DKIM) public key using a Standard DNSDB Search.
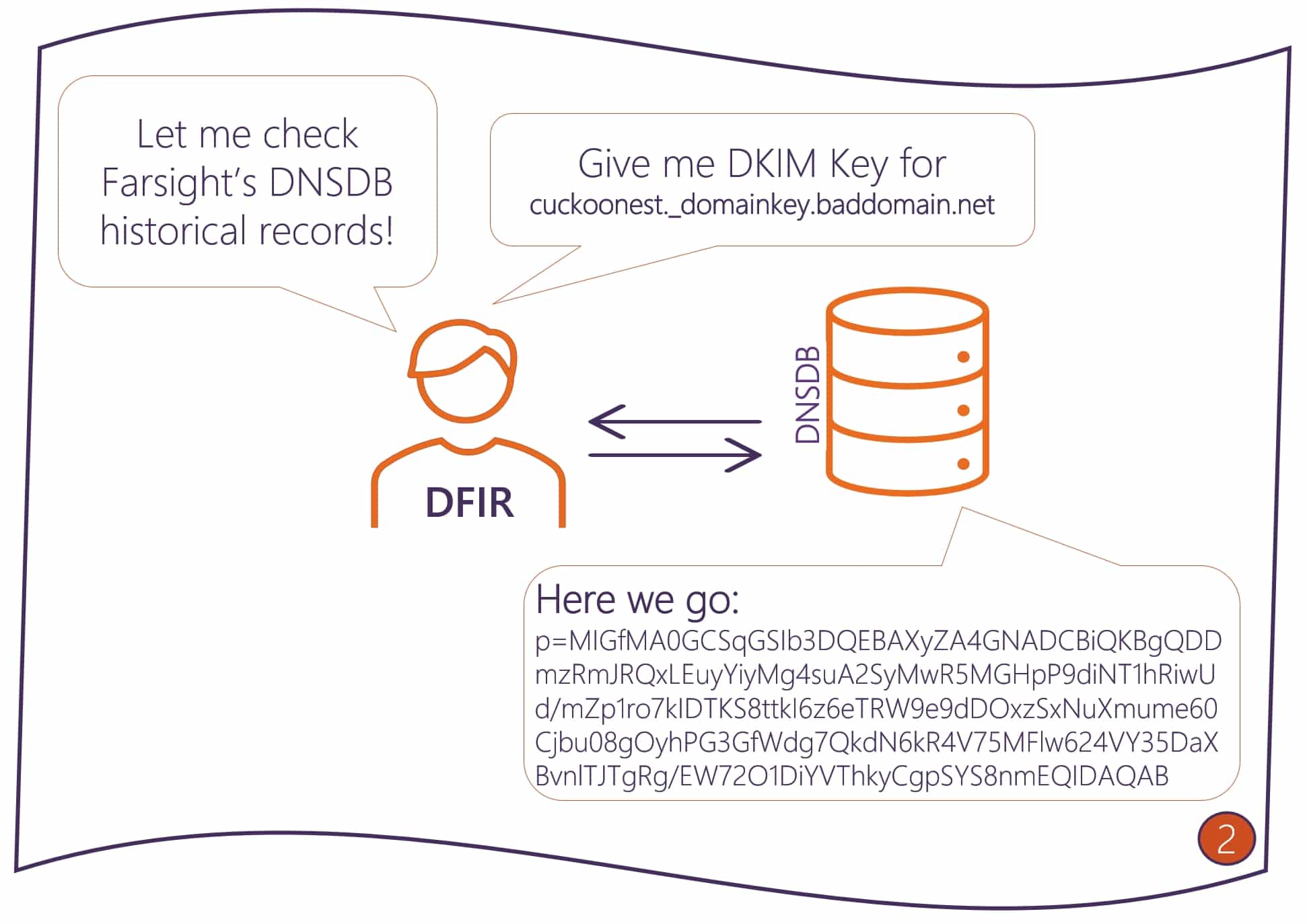
Why is this information important? Because it will help us identify other domains that have used or are using the same key – this will give us an insight on the magnitude of the malicious activity related to that email. By making a Flexible DNSDB Search with the key string as a regular expression, we now can uncover all domains that share the same DKIM key — and all of them look suspicious! We see domains that do not exist anymore as well as those that are live on the Internet. For the latter, you can take proactive measures to defend your organisation by implementing blocks at Response Policy Zone (RPZ) on your DNS firewall. Farsight offers a Newly Observed Domains (NOD) RPZ solution.
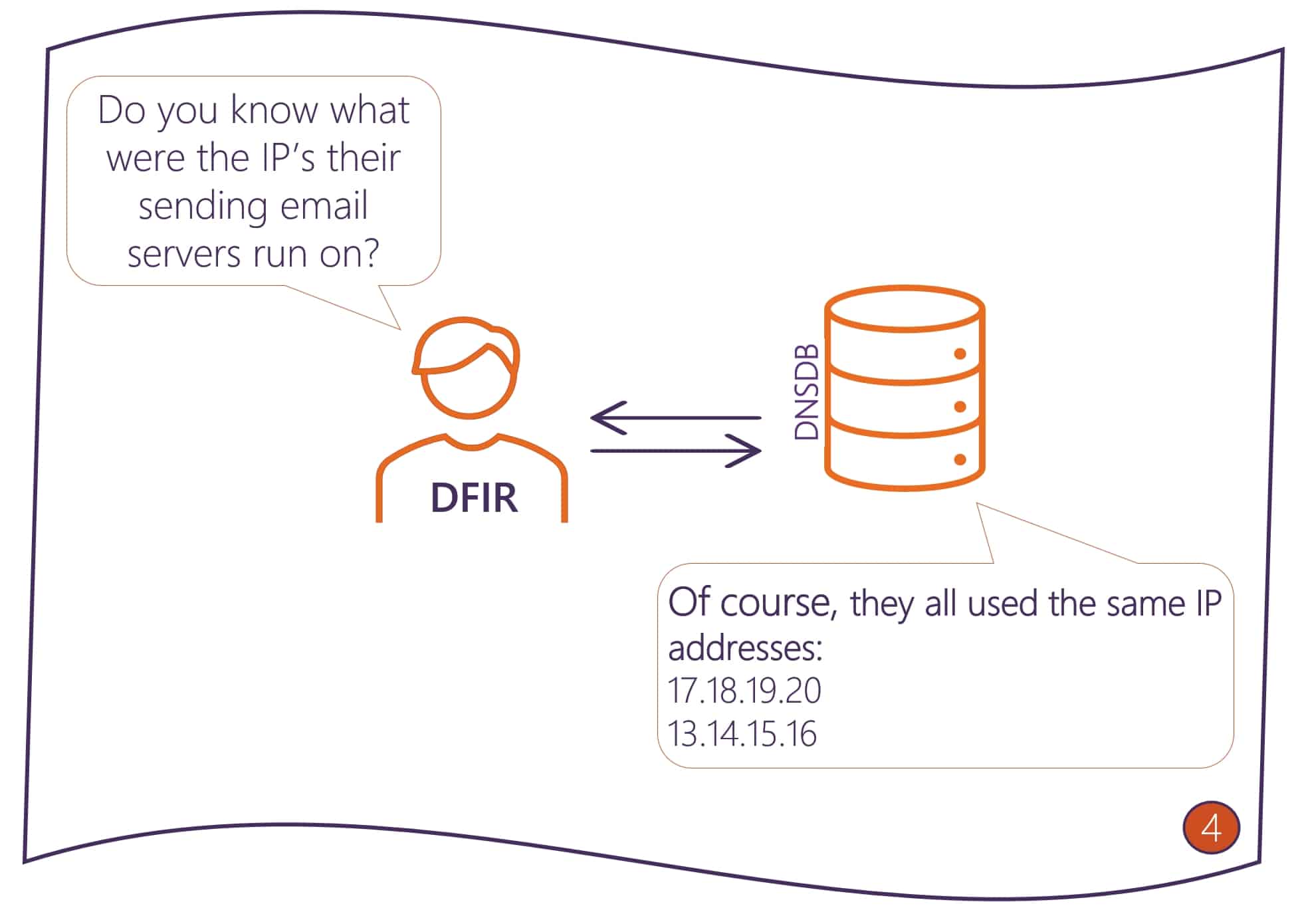
We can go even further! Knowing that perpetrators use DMARC to disguise themselves, we can search Passive DNS – specifically Farsight DNSDB – to identify the email servers that are allowed to emit emails on their behalf. By looking at the Sender Policy Framework (SPF) record using standard DNSDB search, we find that that all those domains share the same two servers hosted on the same IPs. Now, by doing additional DNS searches, we can uncover the extent of the campaign. With this new intelligence, you can now provide your operational teams with IPs to be blocked from receiving emails from by your email exchange.
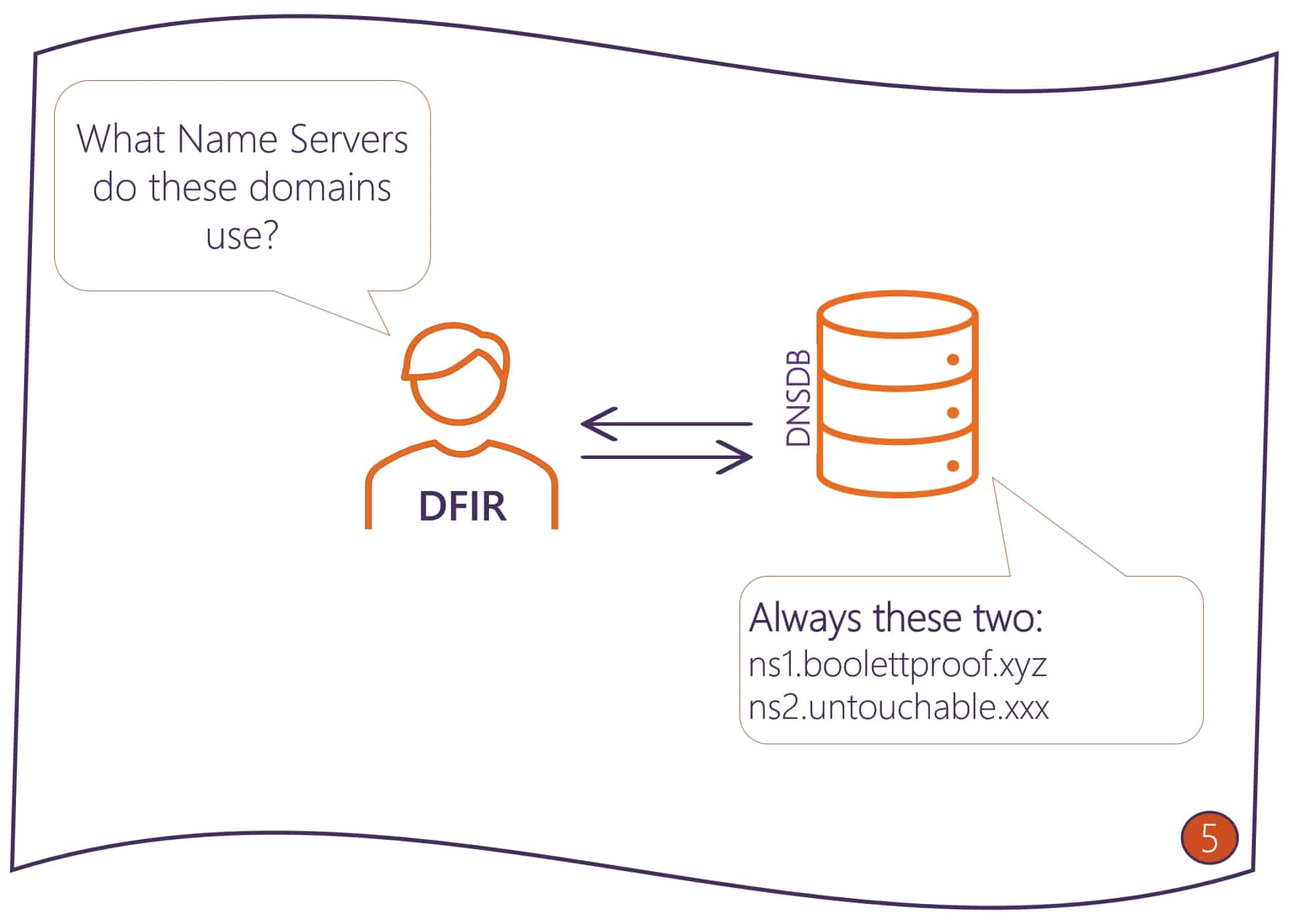
It does seem like a well-organised campaign and you might be wondering whether you uncovered the full extent? Is there is anything more you can do to progress with your investigation? Yes, you can. You can uncover all domains that might be linked to that activity. For that, you need to identify the name servers that serve the domains you already uncovered using Standard DNSDB Search.
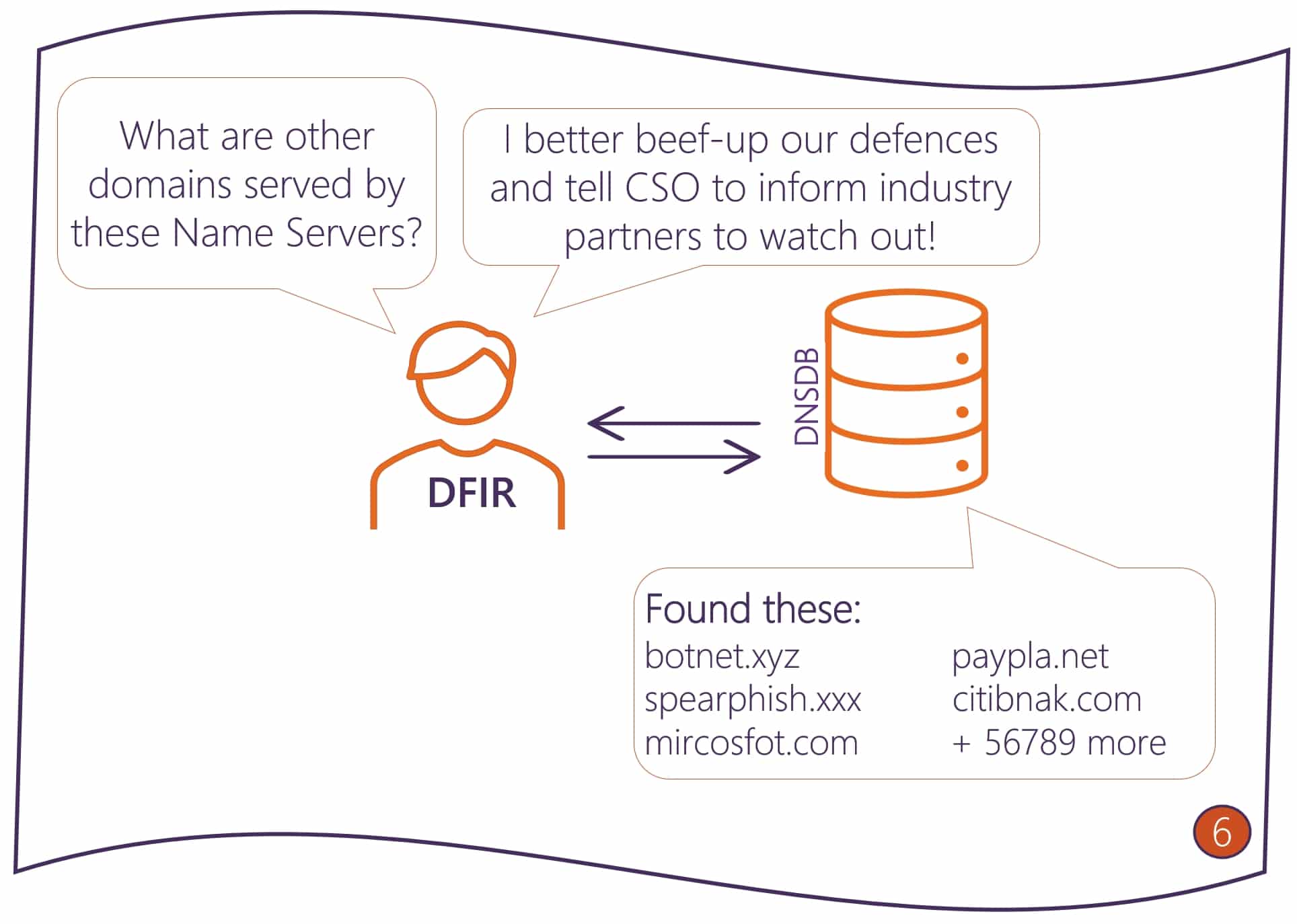
And then, using Standard DNSDB Search again, you can finally identify all the domains that were or are being served by those, likely malicious, name servers. Now you have information that you can pass not only to your DNS firewall team, but also to your threat hunting team to look for other threats that are posed by the domains you uncovered, to your security operations team to check the logs on the presence of those domains that do not exist anymore to search for any indicators of compromise, and to your antifraud and brand protection teams to protect your customers. Of course, it will also be plenty of work for your digital forensics team.
At the completion of the investigation, the CSO can demonstrate how, with the help of DNS Search, the security team not only stayed ahead of current threats, but helped prevent future attacks that could significantly impact business continuity, revenue and brand reputation. The investigation can be also used to proactively build a business case to present to the Board and, with the help of CEO, secure budget for the following year.